Recently I was very fortunate to be able to attend not only the BSides Austin conference this past weekend, but the two training days immediately preceding it. One of the training workshops I attended was Incident Response with Volatility Framework, taught by Evan Wagner. If you ever have the opportunity to attend this training in person, I highly recommend it.
Going into this I had zero experience with digital forensics and had not heard of the Volatility Framework outside of occasional passing references on Twitter. This was, in every sense of the word, my first introduction to this type of thing and I had a lot of fun figuring it out.
The following is a basic introduction to the Volatility Framework as I learned it. I still have a long way to go to really get my feet under me, but hopefully this may be able to help you get started as well.
Software Used
- Oracle VirtualBox version 5.2.8
- Kali Linux 64-bit version 2019.1a
- Volatility 2.6 source code
- NIST Windows XP laptop .vmem file
I am running the setup above on my Windows 8.1 host. The actual versions of the VirtualBox, Kali VM, and Windows host versions you use honestly should not matter too much for this, and in fact the host could be completely different from mine. The primary difference will likely be mostly in the Volatility Framework version selected; earlier (or later) versions may offer different plugin options than the examples shown here.
Summary
Below is a high-level breakdown of the steps detailed in this article:
- Download the Volatility Framework source files
- Unzip volatility-master folder to home directory and rename it volatility
- Test vol.py function with the –info argument
- Run the imageinfo plugin against your .vmem file
- Determine the running processes from your system file with the pslist plugin
This makes a couple of basic assumptions: you are either natively running Linux on your machine bare metal or can set up a Linux virtual machine (VM) on your host; and, whichever the case above may be, you have Python installed in your Linux environment.
If you do not know how to do this, I may add an article in the future about configuring a Kali Linux VM, but for now try Googling it. Half of working in IT is, after all, just plugging things into a search engine and finding the result you need.
In general it is better to run Linux installed natively on your machine rather than through a VM whenever possible. You may have performance issues when working with larger files on a VM versus working those same files when working with a natively installed operating system.
Full disclosure: The first time I did this was using Kali installed directly onto a laptop with 8GB of RAM and I didn’t have any problems. When I went back to retrace these steps for this article on a Kali VM from my Windows laptop, I had significant issues simply extracting and moving the system image files. Eventually I was able to resolve this by configuring the VM to use a static size (not dynamically allocated) Virtual Hard Drive file of 10GB plus allocating 4GB of memory.
Details
Step 1 – Download the Volatility Framework
First, download the Volatility Framework 2.6 Source Code (.zip) file from the Volatility Foundation at the following address:
https://www.volatilityfoundation.org/26
At this point you should also download a memory sample if you don’t have one already. Luckily the Volatility Foundation has a wiki page dedicated to memory samples you can use:
https://github.com/volatilityfoundation/volatility/wiki/Memory-Samples
In this example, I downloaded the Malware – Cridex archive and extracted it into my Volatility folder during Step 2 below.
Step 2 – Unzip and Rename the Volatility Folder
Using your preferred method, unzip the volatility-2.6.zip file, then rename the volatility-master folder included within it to volatility. Once you have your volatility folder ready to go, move that folder into the Home directory, so that when you call the program going forward the path is ~/volatility/.
By itself, this renaming and relocation of folders is not absolutely necessary; it just simplifies the later command syntax a little bit.
Most true Linux neckbeards will probably urge you to complete all of this work through the terminal. Myself, as a heretical Windows user, I heavily utilized my right-click button in the GUI to extract, rename, and relocate the folder.
I also extracted the cridex-memdump.zip file, renamed the resulting folder to cridex, and then moved that folder to ~/volatility/cridex/.
Step 3 – Test Run Volatility
Now that you have everything downloaded, renamed, and moved around, you can try running Volatility for the first time.
Since Volatility is essentially a Python program, you will be using the python command in a terminal window, followed by the vol.py script and some sort of option. In this case we are going to run it using the –info option to display the registered options:
Input:
python ~/volatility/vol.py --info
Output:
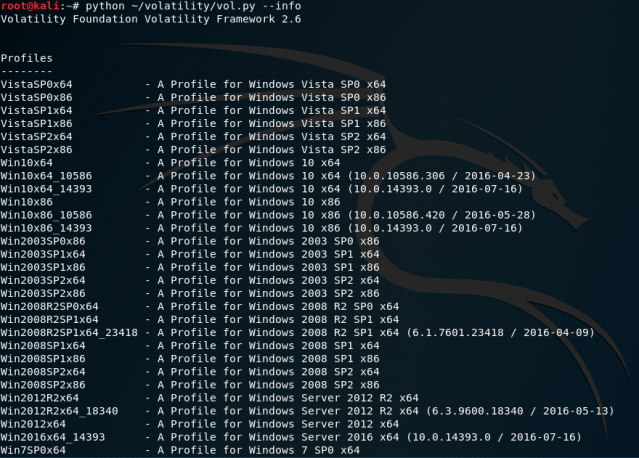
If your window shows a long list of output similar to the above, congratulations — you’ve got a working Volatility setup in place!
Step 4 – Determine the Image Profile of Your Memory Sample
From here, you need to run the imageinfo plugin against your memory sample in order to ascertain the recommended operating system profile to use. In order to set the memory file in the path, it is necessary to run the -f option followed by the actual path of the file being referenced.
Input:
python ~/volatility/vol.py -f ~/volatility/cridex/cridex.vmem imageinfo
Output:

The profile you’re going to want to use is listed in the output from the command above — in this case, WinXPSP2x86.
Step 5 – Find the Running Processes of Your Memory Sample
From here, we can now begin examining the memory sample. After setting our profile with the –profile option, we are going to get a process list from the sample by using the pslist plugin.
Input:
python ~/volatility/vol.py -f ~/volatility/cridex/cridex.vmem --profile=WinXPSP2x86 pslist
Output:

For a true investigation we would probably want to save this to a text file that could be included with any subsequent reporting. We can do this by adding the carrot (‘ > ‘) symbol, followed by a path to and name of a file — such as ~/volatility/cridex/pslist.txt.
In full:
python ~/volatility/vol.py -f ~/volatility/cridex/cridex.vmem --profile=WinXPSP2x86 pslist > ~/volatility/cridex/pslist.txt
From here we can use the cat command to show the contents of our pslist.txt file, and transfer that file as needed for future reporting.

In Conclusion
At this point, you have downloaded Volatility, gotten it ready for use on your system, and run a couple of basic commands to identify the recommended profile for and process list of a sample memory image.
From here you can use the –info option to show you the full list of available plugins that can be used against your memory sample. Some experimentation is required…as is a basic understanding of the operating system in question.
Recommended Reading
- The Art of Memory Forensics: Detecting Malware and Threats in Windows, Linux, and Mac Memory by Michael Hale Ligh, Andrew Case, Jamie Levy, and Aaron Walters (Wiley)
